Vault integration for Grafana Cloud
HashiCorp Vault secures, stores, and controls access to tokens, passwords, certificates, API keys, and other secrets in modern computing. This integration allows you to monitor metrics from Vault.
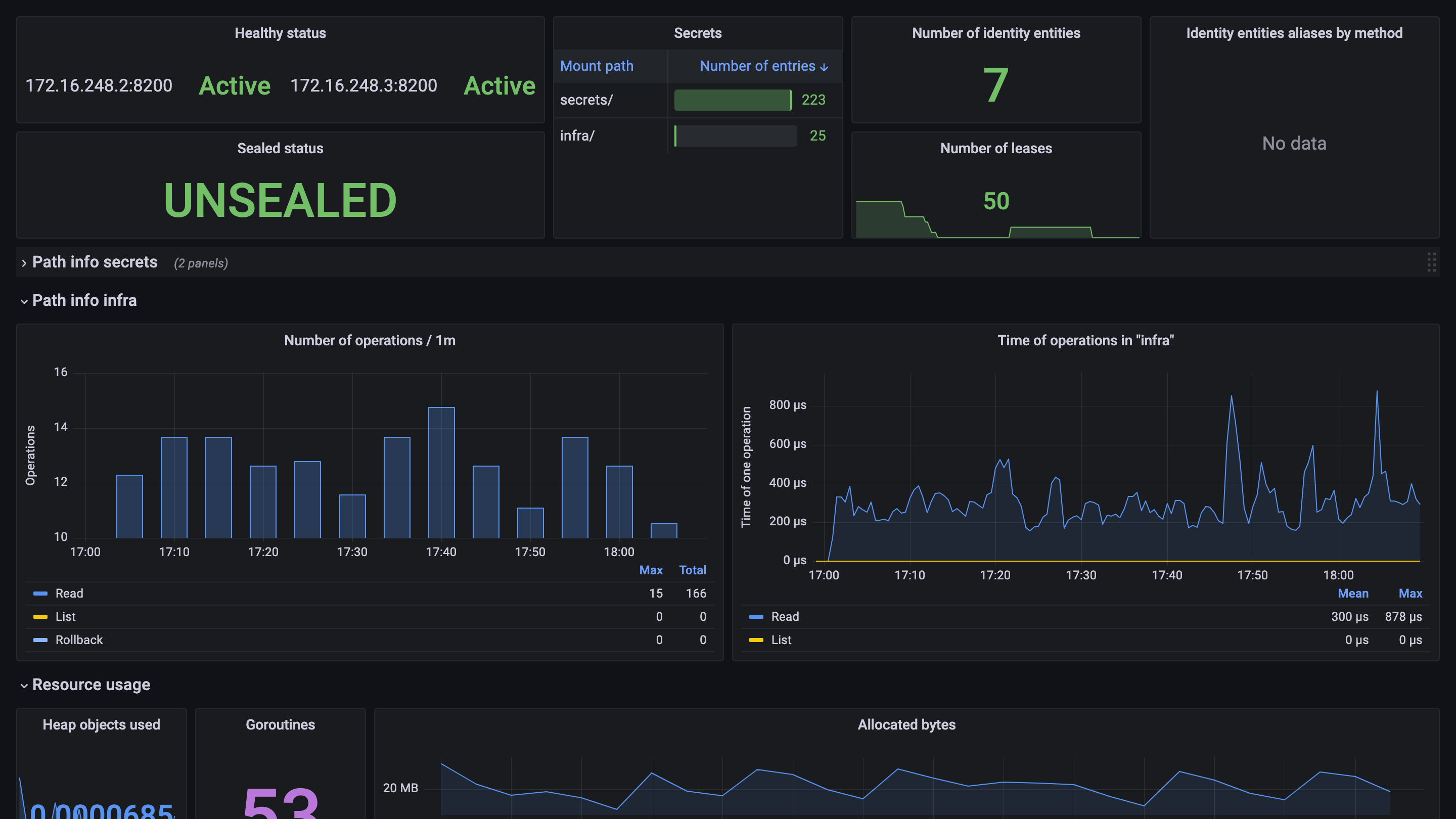
This integration includes 1 pre-built dashboard to help monitor and visualize Vault metrics.
Before you begin
To enable the Prometheus metrics endpoint, you need to activate it in your Vault node.
To do so, add the following snippet to your node configuration file.
telemetry {
disable_hostname = true
prometheus_retention_time = "12h"
}It is also necessary to issue an auth token for Prometheus to scrape the metrics endpoint, which is protected. For further guidance, refer to the official Vault documentation provided in this section.
Install Vault integration for Grafana Cloud
- In your Grafana Cloud stack, click Connections in the left-hand menu.
- Find Vault and click its tile to open the integration.
- Review the prerequisites in the Configuration Details tab and set up Grafana Agent to send Vault metrics to your Grafana Cloud instance.
- Click Install to add this integration’s pre-built dashboard to your Grafana Cloud instance, and you can start monitoring your Vault setup.
Configuration snippets for Grafana Alloy
Simple mode
These snippets are configured to scrape a single Vault instance running locally with default ports.
First, manually copy and append the following snippets into your alloy configuration file.
Metrics snippets
discovery.relabel "metrics_integrations_integrations_vault" {
targets = [{
__address__ = "localhost:8200",
}]
rule {
target_label = "instance"
replacement = constants.hostname
}
}
prometheus.scrape "metrics_integrations_integrations_vault" {
targets = discovery.relabel.metrics_integrations_integrations_vault.output
forward_to = [prometheus.remote_write.metrics_service.receiver]
job_name = "integrations/vault"
params = {
format = ["prometheus"],
}
metrics_path = "/v1/sys/metrics"
authorization {
type = "Bearer"
credentials_file = "/etc/prometheus/prometheus-token"
}
}Advanced mode
The following snippets provide examples to guide you through the configuration process.
To instruct Grafana Alloy to scrape your Vault instances, manually copy and append the snippets to your alloy configuration file, then follow subsequent instructions.
Advanced metrics snippets
discovery.relabel "metrics_integrations_integrations_vault" {
targets = [{
__address__ = "localhost:8200",
}]
rule {
target_label = "instance"
replacement = constants.hostname
}
}
prometheus.scrape "metrics_integrations_integrations_vault" {
targets = discovery.relabel.metrics_integrations_integrations_vault.output
forward_to = [prometheus.remote_write.metrics_service.receiver]
job_name = "integrations/vault"
params = {
format = ["prometheus"],
}
metrics_path = "/v1/sys/metrics"
authorization {
type = "Bearer"
credentials_file = "/etc/prometheus/prometheus-token"
}
}To monitor your Vault instance, you must use a discovery.relabel component to discover your Vault Prometheus endpoint and apply appropriate labels, followed by a prometheus.scrape component to scrape it.
Configure the following properties within each discovery.relabel component:
__address__: The address to your Vault Prometheus metrics endpoint.instancelabel:constants.hostnamesets theinstancelabel to your Grafana Alloy server hostname. If that is not suitable, change it to a value uniquely identifies this Vault instance.
If you have multiple Vault servers to scrape, configure one discovery.relabel for each and scrape them by including each under targets within the prometheus.scrape component.
Grafana Agent static configuration (deprecated)
The following section shows configuration for running Grafana Agent in static mode which is deprecated. You should use Grafana Alloy for all new deployments.
Before you begin
To enable the Prometheus metrics endpoint, you need to activate it in your Vault node.
To do so, add the following snippet to your node configuration file.
telemetry {
disable_hostname = true
prometheus_retention_time = "12h"
}It is also necessary to issue an auth token for Prometheus to scrape the metrics endpoint, which is protected. For further guidance, refer to the official Vault documentation provided in this section.
Install Vault integration for Grafana Cloud
- In your Grafana Cloud stack, click Connections in the left-hand menu.
- Find Vault and click its tile to open the integration.
- Review the prerequisites in the Configuration Details tab and set up Grafana Agent to send Vault metrics to your Grafana Cloud instance.
- Click Install to add this integration’s pre-built dashboard to your Grafana Cloud instance, and you can start monitoring your Vault setup.
Post-install configuration for the Vault integration
After enabling the metrics generation and setting up an authorization method, instruct Grafana Agent to scrape your Vault nodes.
Vault exposes a /v1/sys/metrics endpoint. To scrape it, add the provided snippet to your agent configuration file.
Make sure to change targets, scheme (http is selected by default) and authorization in the snippet according to your environment.
Configuration snippets for Grafana Agent
Below metrics.configs.scrape_configs, insert the following lines and change the URLs according to your environment:
- job_name: integrations/vault
metrics_path: /v1/sys/metrics
params:
format: ['prometheus']
scheme: http
authorization:
credentials_file: /etc/prometheus/prometheus-token
relabel_configs:
- replacement: '<your-instance-name>'
target_label: instance
static_configs:
- targets: ['localhost:8200']Full example configuration for Grafana Agent
Refer to the following Grafana Agent configuration for a complete example that contains all the snippets used for the Vault integration. This example also includes metrics that are sent to monitor your Grafana Agent instance.
integrations:
prometheus_remote_write:
- basic_auth:
password: <your_prom_pass>
username: <your_prom_user>
url: <your_prom_url>
agent:
enabled: true
relabel_configs:
- action: replace
source_labels:
- agent_hostname
target_label: instance
- action: replace
target_label: job
replacement: "integrations/agent-check"
metric_relabel_configs:
- action: keep
regex: (prometheus_target_sync_length_seconds_sum|prometheus_target_scrapes_.*|prometheus_target_interval.*|prometheus_sd_discovered_targets|agent_build.*|agent_wal_samples_appended_total|process_start_time_seconds)
source_labels:
- __name__
# Add here any snippet that belongs to the `integrations` section.
# For a correct indentation, paste snippets copied from Grafana Cloud at the beginning of the line.
logs:
configs:
- clients:
- basic_auth:
password: <your_loki_pass>
username: <your_loki_user>
url: <your_loki_url>
name: integrations
positions:
filename: /tmp/positions.yaml
scrape_configs:
# Add here any snippet that belongs to the `logs.configs.scrape_configs` section.
# For a correct indentation, paste snippets copied from Grafana Cloud at the beginning of the line.
metrics:
configs:
- name: integrations
remote_write:
- basic_auth:
password: <your_prom_pass>
username: <your_prom_user>
url: <your_prom_url>
scrape_configs:
# Add here any snippet that belongs to the `metrics.configs.scrape_configs` section.
# For a correct indentation, paste snippets copied from Grafana Cloud at the beginning of the line.
- job_name: integrations/vault
metrics_path: /v1/sys/metrics
params:
format: ['prometheus']
scheme: http
authorization:
credentials_file: /etc/prometheus/prometheus-token
relabel_configs:
- replacement: '<your-instance-name>'
target_label: instance
static_configs:
- targets: ['localhost:8200']
global:
scrape_interval: 60s
wal_directory: /tmp/grafana-agent-walDashboards
The Vault integration installs the following dashboards in your Grafana Cloud instance to help monitor your system.
- Hashicorp Vault
Vault overview
Metrics
The most important metrics provided by the Vault integration, which are used on the pre-built dashboard, are as follows:
- up
- vault_audit_log_request_count
- vault_audit_log_request_failure
- vault_audit_log_response_count
- vault_audit_log_response_failure
- vault_consul_delete_count
- vault_consul_get_count
- vault_consul_list_count
- vault_consul_put_count
- vault_core_active
- vault_core_handle_request_count
- vault_core_unsealed
- vault_expire_num_leases
- vault_identity_num_entities
- vault_policy_get_policy_count
- vault_policy_set_policy_count
- vault_runtime_alloc_bytes
- vault_runtime_heap_objects
- vault_runtime_malloc_count
- vault_runtime_num_goroutines
- vault_secret_kv_count
- vault_token_count
- vault_token_count_by_auth
- vault_token_count_by_policy
- vault_token_count_by_ttl
- vault_token_create_count
- vault_token_creation
- vault_token_lookup_count
- vault_token_store_count
Changelog
# 0.0.4 - September 2023
* New Filter Metrics option for configuring the Grafana Agent, which saves on metrics cost by dropping any metric not used by this integration. Beware that anything custom built using metrics that are not on the snippet will stop working.
* New hostname relabel option, which applies the instance name you write on the text box to the Grafana Agent configuration snippets, making it easier and less error prone to configure this mandatory label.
# 0.0.3 - December 2022
* Change panels to timeseries
* Change old bar charts to new bar gauges
* Add job, instance selectors
* Fix secrets table, add gauge to the table
# 0.0.2 - October 2022
* Updating mixin with the latest piechart panel
# 0.0.1 - October 2021
* Initial releaseCost
By connecting your Vault instance to Grafana Cloud, you might incur charges. To view information on the number of active series that your Grafana Cloud account uses for metrics included in each Cloud tier, see Active series and dpm usage and Cloud tier pricing.
Was this page helpful?
Related resources from Grafana Labs



